Introducing the first AI-native CRM
Connect your email, and you’ll instantly get a CRM with enriched customer insights and a platform that grows with your business.
With AI at the core, Attio lets you:
Prospect and route leads with research agents
Get real-time insights during customer calls
Build powerful automations for your complex workflows
Join industry leaders like Granola, Taskrabbit, Flatfile and more.
Want to appear here? Talk with us
Critical Vulnerability
Fortinet’s delayed alert on actively exploited defect put defenders at a disadvantage
A severe vulnerability in Fortinet’s FortiWeb firewall (CVE 2025‑64446) was being exploited in the wild before many customers knew.
Fortinet pushed a silent patch on October 28 but didn’t assign a CVE or issue a public alert until 17 days later — by then active attacks were underway.
Researchers say attackers used the flaw to add admin accounts, creating persistent, privileged access.
Problems with Vendor Transparency
Security teams are upset. Delayed public disclosure undermines defenders’ ability to react quickly.
Fortinet justified its delay by saying they communicate directly with affected customers.
But several defenders argue that “silent patching” put too much of a burden on teams that didn’t know how urgent the fix was.
New Flaw Adds to the Chaos
Soon after the first bug, another was disclosed: CVE‑2025‑58034 — this is an OS command injection vulnerability.
Fortinet fixed both bugs in the same update (8.0.2), but because of the staggered public disclosure, defenders now face two zero-days in rapid succession.
CISA has added both vulnerabilities to its Known Exploited Vulnerabilities catalog.
Why This Matters for Security Teams
When security vendors delay telling customers about dangerous flaws, it can leave teams blind and vulnerable.
Quick, clear, and public disclosure helps defenders prioritize patching and threat response.
Fortinet’s approach here raises big questions about how vulnerability management and vendor transparency should work—and how much companies should trust “silent” fixes.
Cyber Risk
Immersive’s 2025 Cyber Workforce Benchmark Report Exposes a Global Readiness Illusion
Most companies (94%) believe they are ready for a big cyber crisis.
But when tested, their real performance is weak: decision accuracy averages just 22%, and it takes about 29 hours to contain attacks in simulations.
On top of that, their “resilience score” — a measure of how well they can handle cyber incidents — is stable or even a little lower than last year.
Training Isn’t Keeping Up
A big part of the problem is that training is out of date: 60% of labs focus on vulnerabilities that are over two years old.
Most teams also stick with very basic drills; only a minority go into advanced scenarios that help develop real “muscle memory.”
Key Players Are Left Out
When cyber drills happen, non-technical roles are often left out. Only 41% of companies include people from departments like HR, Legal, or Communications.
That’s a problem, because when a real crisis hits, collaboration across all teams matters — not just the security team.
New Threats, Old Habits
Experienced cyber staff do well in classic drill scenarios (around 80% accuracy), but they struggle with newer threats — like AI-driven or novel attack styles.
Participation in labs focused on AI threats is actually going down, even though adversaries are likely to use those very techniques.
What This Means
There’s a big gap between what leaders think their teams can do, and what the data shows they actually can do under pressure. Real resilience takes more than confidence — it needs proven skills, realistic drills, and consistent testing.
Readiness isn’t just about training; it’s about earning trust through real, measurable experience.
📺️ Podcast
Who Really Pays When the Cloud Fails? Inside the October 2025 AWS Outage
In this episode of the Microsoft Threat Intelligence Podcast, host Sherrod DeGrippo is joined by security researchers Tori Murphy and Anna Seitz to unpack two financially motivated cyber threats.
First, they explore the Payroll Pirates campaign (Storm 2657), which targets university payroll systems through phishing and MFA theft to reroute direct deposits.
Then, they examine Vanilla Tempest, a ransomware group abusing fraudulent Microsoft Teams installers and SEO poisoning to deliver the Oyster Backdoor and Recita ransomware.
DDoS
'Largest-ever' cloud DDoS attack pummels Azure with 3.64B packets per second
On October 24, 2025, Azure faced what Microsoft calls the largest-ever cloud DDoS attack — 15.72 Tbps, flooding at nearly 3.64 billion packets per second.
Over 500,000 IP addresses were involved, coming from an IoT botnet called Aisuru.
The traffic was mostly UDP floods, targeting a single endpoint in Australia.
How Azure Responded
Azure’s built-in DDoS Protection service caught the attack automatically.
Thanks to its global filtering network, the malicious traffic was redirected and filtered — and none of Microsoft’s customer workloads were disrupted.
Why It’s Important
The attack shows how dangerous large-scale botnets can be, especially when they use compromised IoT devices.
It also highlights that even cloud‑scale services are not immune — but strong automated defense systems can still protect critical infrastructure.
Azure’s ability to absorb this flood without downtime underscores how critical robust DDoS defenses are for modern cloud environments.
Data Leakage
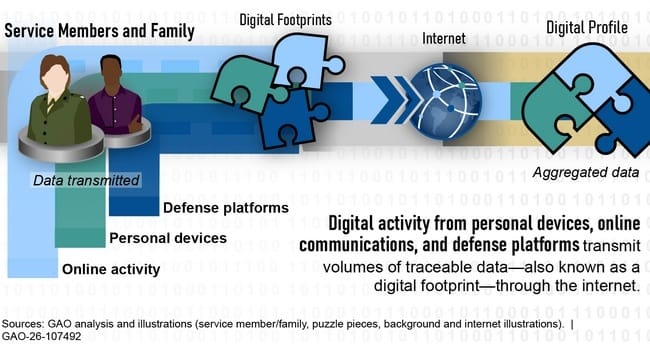
Pentagon and soldiers let too many secrets slip on social networks, watchdog says
A watchdog (GAO) found that many U.S. service members and their families share too much sensitive information on social media.
Auditors posed as bad actors and showed they could gather real intel — like family ties, deployment info, and unit locations — from public posts.
That kind of data could be used for blackmail or to track military operations.
Training and Guidance Gaps
Many parts of the Department of Defense do not train their people well on how to protect their digital footprint.
The GAO notes that some units ignore key security areas like insider risk and force protection.
The policy team at the Pentagon has not done enough to guide how personnel and their families should behave online.
Reforming for Real Threats
The GAO made 12 suggestions to improve how the DoD handles digital risk.
They want better threat assessments, better training, and more consistent rules on what can be shared.
The Department agrees with most of the recommendations — but pushed back on controls tied to personal social media use.
Why This Matters for Security Teams
Even powerful organizations can be exposed by what their people and their families post online.
Bad actors could piece together public data to map out sensitive profiles and target individuals.
Stronger training and clear policies are needed now — because in today’s world, even a social media post can be a security risk.
Report
Delinea Report Finds Identity Security Controls Now Central to Cyber Insurance Coverage Decisions
Identity controls are becoming a key factor for cyber insurance coverage.
Nearly all organizations surveyed said these controls affect premiums or eligibility.
Privileged Access Management leads as the most important measure, followed by Identity Governance and third-party access controls.
Impact of Incidents
Almost half of claim-triggering incidents involved identity issues or privileged account compromises.
This shows insurers are closely monitoring how organizations manage access and identities.
AI's Role in Coverage
AI adoption influences insurance costs.
Many organizations reported lower premiums due to AI-driven security tools like threat detection and behavior monitoring.
However, some policies now exclude coverage for AI misuse.
Conclusion
Strong identity security is no longer optional—it directly affects cyber insurance terms and cost. Organizations must demonstrate solid identity management to maintain coverage and control expenses.
Stay safe!